/*! elementor – v3.7.7 – 20-09-2022 */
.elementor-widget-image{text-align:center}.elementor-widget-image a{display:inline-block}.elementor-widget-image a img[src$=”.svg”]{width:48px}.elementor-widget-image img{vertical-align:middle;display:inline-block}
Standardizing interfaces is nothing new to the technology world. USB-C, 802.11a/g/n, CAT-6 and RG-59 have all been successfully adopted as standards in the products we use every day. These standards serve a vital purpose in enabling seamless integration of new technology into our lives, be connecting your phone to a coffee house wifi, or hooking up a new monitor to your laptop.
Space Systems on the other hand have notoriously been lacking in standards. Launch systems have successfully enforced standards on payload adapters, but interfaces between systems and individual components continue to be driven by mission specific requirements.
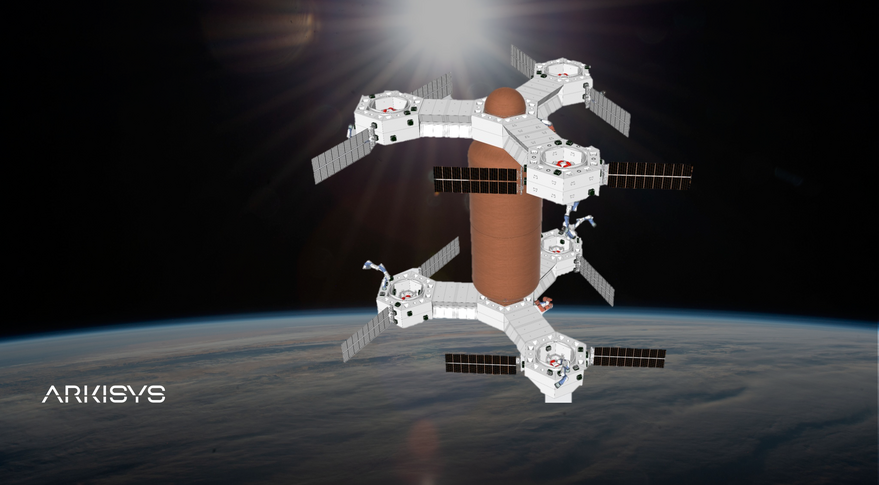
A lot can be said about the feasibility of standards in Space Systems as they exist today. For the purpose of this article, lets assume that Arkisys is able to deliver and their universal interface adapter is adopted by the community at large. The question we want is discuss is “What are the Cyber Security implications of this new standard?”
/*! elementor – v3.7.7 – 20-09-2022 */
.elementor-heading-title{padding:0;margin:0;line-height:1}.elementor-widget-heading .elementor-heading-title[class*=elementor-size-]>a{color:inherit;font-size:inherit;line-height:inherit}.elementor-widget-heading .elementor-heading-title.elementor-size-small{font-size:15px}.elementor-widget-heading .elementor-heading-title.elementor-size-medium{font-size:19px}.elementor-widget-heading .elementor-heading-title.elementor-size-large{font-size:29px}.elementor-widget-heading .elementor-heading-title.elementor-size-xl{font-size:39px}.elementor-widget-heading .elementor-heading-title.elementor-size-xxl{font-size:59px}
Security by Obscurity
One of the advantages to having a Space System that is designed in house from the ground up is that the inner workings of the system are not known to the adversary. The threat actor will also typically lack a system on which to test their malicious commands or software against as the only one in existence is in your teams control, or in orbit. This greatly reduces the impact of any potential attacks as well as gives security teams strong indicators of potential compromise should the attacker start testing against the production machine.
A universal interface/standard removes this element from play by providing attackers with important information regarding how your system will accept, authenticate, and process requests. Even if a standard is considered secure, an attacker will eventually find a flaw that enables them to bypass the security in the system and take control of the Space Vehicle. This can actually have a compounding impact as the designers of the system may incorrectly assume that since the standard is secure, they can cut corners and implement less security on the back end. We’ve seen this occur every time a new 0 day is dropped for an important standard.
Malicious Interfaces
As interface standards become more common and trusted, they begin to open new doors for attackers when developers rely too heavily on the authenticity of the interface. For example, a threat actor could launch a malicious payload posing as any subsystem or component of a satellite. They could use that payload to inject malicious hardware or software onto the universal adapter ahead of a rendezvous with the target in order to take control of the target Space Vehicle.
We see these sorts of attacks in terrestrial life frequently with credit card skimmers. Skimmers are devices that sit flush against a credit card reader and read your cards information as the device is processing your purchase. The attacker is then transmitted your credit card information remotely. This attack is enabled by the standard design of credit card readers
Original Article: https://spacenews.com/arkisys-applique/